The LDAP integration with Webdam should be handled by the company’s LDAP admin. The LDAP admin will require a Webdam account with admin privileges.
- Log into Webdam as an admin.
http://company.webdamdb.com/splash.php
*the domain highlighted in red should be replaced with your webdam domain.
- Access the Webdam LDAP configuration
Settings-> System Preferences -> LDAP Settings (left navigation menu)
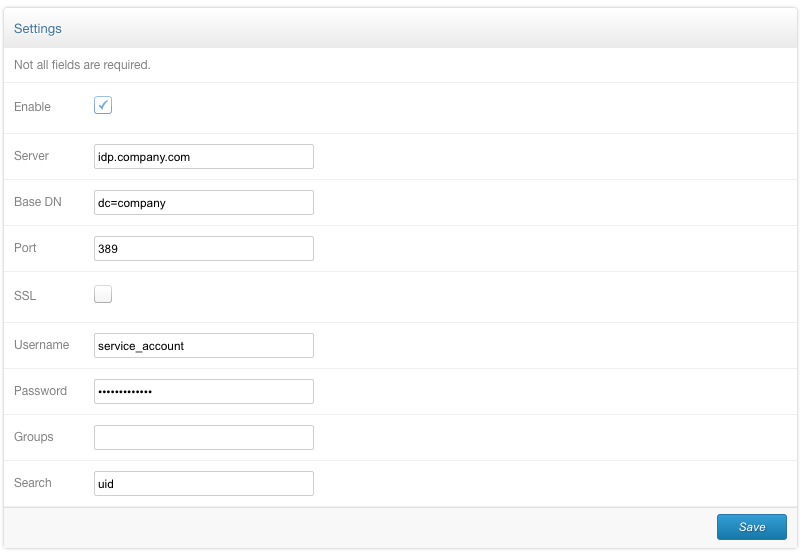
- Provide LDAP Server settings to establish an LDAP connection from Webdam:
Enable: Enable LDAP authentication for Webdam (enable once LDAP configuration is completed and tested)
Server: LDAP server hostname or IP address (ex. ldap.company.com)
Base DN: Search Base DN (ex: ou=users, dc=company ,dc=com)
Port: 389/636. Make sure to enable proper firewall access to Webdams production IP addresses (52.70.22.230,52.70.142.178)
SSL: Check if SSL LDAP port is in use.
Username: The Bind DN (ex: service_account or cn=service_account, ou=admin, dc=company, dc=com). OPTIONAL. Not necessary for anonymous bind.
Password: Password for Bind DN. OPTIONAL. Not necessary for anonymous bind.
Groups: Group Membership of the LDAP user account (ex: users). OPTIONAL. This is rarely used.
Search: Attribute to locate LDAP user account. (ex: uid). For Active Directory setups, use sAMAccountName.
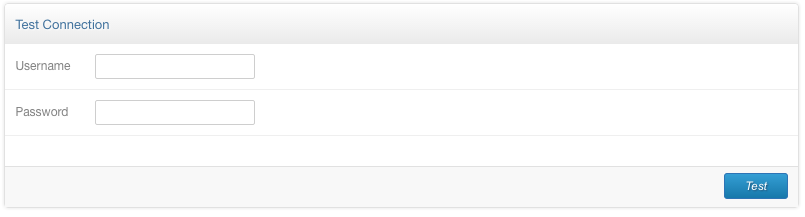
- Use Test Connection to test LDAP settings were properly configured. Supply test LDAP credentials.
|
Message |
Description |
|
Success. Was able to connect and authenticate user |
LDAP configuration is successful. LDAP authentication is ready to be enabled in Webdam. |
|
LDAP error message: (-1) - Can't contact LDAP server |
Webdam is unable to connect to LDAP server. Allow proper firewall access to LDAP server and LDAP port for Webdam’s Production IP addresses |
|
LDAP error message: (34) - Invalid DN syntax |
Bind DN is misconfigured. Supply proper Bind DN credentials or remove for Anonymous binds. |
|
LDAP error message: (49) - Invalid credentials |
Supplied LDAP credentials may be incorrect. Submit proper LDAP credentials. The attribute search may also be incorrect. Make to supply correct attribute to locate LDAP account. |
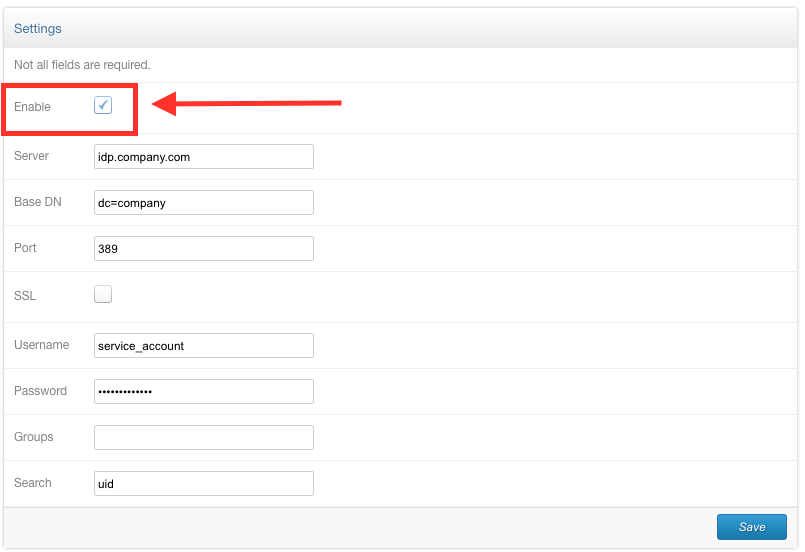
- Enable LDAP authentication in Webdam. Once LDAP configuration has been verified using the Test Connection box, enable LDAP by checking the Enable box in the Settings box.
Verify LDAP login is properly working in Webdam
- Use the following URL to test LDAP login:
http://company.webdamdb.com/splash.php
*remember to use your webdam domain
- Provide LDAP credentials in the login box. If login is successful, user should connect into Webdam authenticated.
*Receiving the “registration successful” notification indicates LDAP authentication was successful, but new user account created in Webdam is set to inactive. To allow new users to automatically log into Webdam, log into Webdam as an admin and navigate to (Settings-> System Preferences), uncheck “New users must be approved after registering”.
- Verify user’s account is automatically created in Webdam by logging into Webdam as an admin. Navigate to (Permissions -> Users) and check the user account exists. If user account is not created and Anonymous Bind is not in use, make sure Bind DN has proper access to the following attributes: username, email, first name, and last name.
Updated
Comments
0 comments
Article is closed for comments.